欢迎大家一起来Hacking水友攻防实验室学习,渗透测试,代码审计,免杀逆向,实战分享,靶场靶机,求关注
HTML注入类似于xss注入但又不是,因为他的威胁程度大于后者,它可以在HTML页面中嵌入如何可以执行的代码,实际上它是所有注入类代码漏洞的鼻祖
目录
HTML Injection - Reflected (GET)
low
medium
high
HTML Injection - Reflected (POST)
HTML Injection - Reflected (URL)
low
medium
high
HTML Injection - Stored (Blog)
low
medium
high
iFrame Injection
low
medium
high
HTML Injection - Reflected (GET)
low
get传递参数,这是由于代码过滤不严格导致的,我们可以在可以输入的first name和last name处注入我们的恶意代码:
<div id="main">
<h1>HTML Injection - Reflected (GET)</h1>
<p>Enter your first and last name:</p>
<form action="<?php echo($_SERVER["SCRIPT_NAME"]);?>" method="GET">
<p><label for="firstname">First name:</label><br />
<input type="text" id="firstname" name="firstname"></p>
<p><label for="lastname">Last name:</label><br />
<input type="text" id="lastname" name="lastname"></p>
<button type="submit" name="form" value="submit">Go</button>
</form>
<br />
<?php
if(isset($_GET["firstname"]) && isset($_GET["lastname"]))
{
$firstname = $_GET["firstname"];
$lastname = $_GET["lastname"];
if($firstname == "" or $lastname == "")
{
echo "<font color=\"red\">Please enter both fields...</font>";
}
else
{
echo "Welcome " . htmli($firstname) . " " . htmli($lastname);
}
}
?>防护代码是no-check,我们构造xss注入可以获取想要的任何信息:</label><script>alert(/xss/)</script>#,,,,成功反弹xss
medium
打开bwapp文件夹下的functions_external.php文件:
function xss_check_1($data)
{
// Converts only "<" and ">" to HTLM entities
$input = str_replace("<", "<", $data);
$input = str_replace(">", ">", $input);
// Failure is an option
// Bypasses double encoding attacks
// <script>alert(0)</script>
// %3Cscript%3Ealert%280%29%3C%2Fscript%3E
// %253Cscript%253Ealert%25280%2529%253C%252Fscript%253E
$input = urldecode($input);
return $input;
}
把左右尖括号过滤,但是没有过滤HTML编码,我们可以进行HTML二次编码绕过:在url后面输入:%253Cscript%253Ealert%25280%2529%253C%252Fscript%253E,,弹出0.一个xss攻击完成。
high
return htmlentities($data, ENT_QUOTES);这个是真的没办法了所有字符都被过滤了。。。
HTML Injection - Reflected (POST)
和get一模一样,不过就是换了一种传参方式而已,用burpsuit神器,然后和get一样照抄就好了。。。
HTML Injection - Reflected (URL)
low
<h1>HTML Injection - Reflected (URL)</h1>
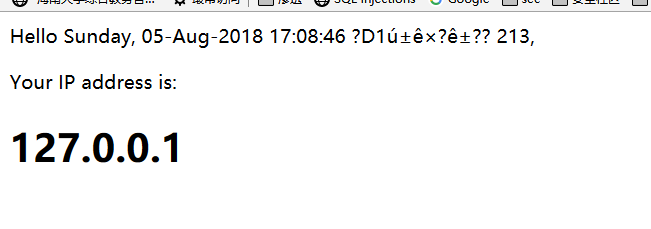
<?php echo "<p align=\"left\">Your current URL: <i>" . $url . "</i></p>";?> 输入什么就会在页面上返回什么:

那么这个url是怎么来的呢?http://+我们主机的ip地址+合法的url虚拟目录。我们可以在burp suit中修改host字段以实现登录到别的ip的bwapp网页
$url = "http://" . $_SERVER["HTTP_HOST"] . $_SERVER["REQUEST_URI"];
我们把host改为192.168.43.185:

我们也可以把第一行的get请求之后的url进行修改,形成一个欺骗,欺骗访客,让他以为自己阅读到了某个内容,但实际上该内容来自另一个文件:

medium
$url = "<script>document.write(document.URL)</script>";弹出这个dom树的URL,无法注入..document对象 :代表整个HTML 文档,可用来访问页面中的所有元素
document.URL:设置URL属性从而在同一窗口打开另一网页
document.write():动态向页面写入内容
high
$url = "http://" . $_SERVER["HTTP_HOST"] . xss_check_3($_SERVER["REQUEST_URI"]);url采用了HTML编码,,无法在url那里绕过,但是可以在后缀加上?id=2,,或者host改变一下,稍微骗一下访客。url已经不可能注入了。
HTML Injection - Stored (Blog)
low
$sql = "INSERT INTO blog (date, entry, owner) VALUES (now(),'" . $entry . "','" . $owner . "')";
$recordset = $link->query($sql);
if(!$recordset)
{
die("Error: " . $link->error . "<br /><br />");
}防护措施是仅仅过滤了/\的转义符号识别函数:
function sqli_check_3($link, $data)
{
return mysqli_real_escape_string($link, $data);
}
那么我们可以构造一个恶意页面钓鱼网站让它自己跳转到那里去:

medium
function xss_check_4($data)
{
// addslashes - returns a string with backslashes before characters that need to be quoted in database queries etc.
// These characters are single quote ('), double quote ("), backslash (\) and NUL (the NULL byte).
// Do NOT use this for XSS or HTML validations!!!
return addslashes($data);addslashes() 函数返回在预定义字符之前添加反斜杠的字符串。
预定义字符是:
- 单引号(')
- 双引号(")
- 反斜杠(\)
- NULL
如果是sql注入还可以利用宽字节等方法绕过, 但html注入就无法注入了。
high
和中等难度一样,无法注入,都被htmlspecialchars转换为实体了……
function xss_check_3($data, $encoding = "UTF-8")
{
// htmlspecialchars - converts special characters to HTML entities
// '&' (ampersand) becomes '&'
// '"' (double quote) becomes '"' when ENT_NOQUOTES is not set
// "'" (single quote) becomes ''' (or ') only when ENT_QUOTES is set
// '<' (less than) becomes '<'
// '>' (greater than) becomes '>'
return htmlspecialchars($data, ENT_QUOTES, $encoding);iFrame Injection
low
<div id="main">
<h1>iFrame Injection</h1>
<?php
if($_COOKIE["security_level"] == "1" || $_COOKIE["security_level"] == "2")
{
?>
<iframe frameborder="0" src="robots.txt" height="<?php echo xss($_GET["ParamHeight"])?>" width="<?php echo xss($_GET["ParamWidth"])?>"></iframe>
<?php
}
else
{
?>
<iframe frameborder="0" src="<?php echo xss($_GET["ParamUrl"])?>" height="<?php echo xss($_GET["ParamHeight"])?>" width="<?php echo xss($_GET["ParamWidth"])?>"></iframe>
<?php
}
?>防护等级low时,三个参数都可以注入。

目录穿越+文件类漏洞:比如把paramurl改为../README.txt,实现父目录中的文件读取:
url跳转:

xss注入:
ParamUrl=" onload="alert(1)&ParamWidth=800&ParamHeight=800 // 闭合注入xss
ParamUrl=javascript:alert(111)&ParamWidth=800&ParamHeight=800 // JavaScript伪协议medium
防护措施:
function xss_check_4($data)
{
// addslashes - returns a string with backslashes before characters that need to be quoted in database queries etc.
// These characters are single quote ('), double quote ("), backslash (\) and NUL (the NULL byte).
// Do NOT use this for XSS or HTML validations!!!
return addslashes($data);
}我们考虑能不能通过url中2个参数自身的“”来闭合绕过(robots.txt已经被写死不能注入了),就从height开始注入:

构造payload:ParamHeight=250"></iframe><script>alert(/xss/)</script>//,成功弹出xss会话框。同理,用width注入也是一样的。这道题的绕过,说明了在\对于数字的大小没有影响。
high
防护措施:
function xss_check_3($data, $encoding = "UTF-8")
{
// htmlspecialchars - converts special characters to HTML entities
// '&' (ampersand) becomes '&'
// '"' (double quote) becomes '"' when ENT_NOQUOTES is not set
// "'" (single quote) becomes ''' (or ') only when ENT_QUOTES is set
// '<' (less than) becomes '<'
// '>' (greater than) becomes '>'
return htmlspecialchars($data, ENT_QUOTES, $encoding);
}
全部转化为HTML实体,所以无法绕过,应该是一个安全的函数保护。QAQ